IAL3 represents the highest standard in identity proofing. This service requires an on-site attended session by a certified CSP representative as well as full biometric capture capabilities and other methods for verification purposes.
Trust Swiftly’s IAL3 solution integrates multiple verification methods in a flexible pay-as-you-go package that eliminates hardware costs and long-term contracts, cutting identity scams by up to 40 percent for companies using this system. Research shows companies using it experience up to 40% fewer identity scams.
NIST 800-63-4 IAL3 Software Benefits
To counter this state-sponsored threat and protect remote IT workers and defense supply chains, an immediate paradigm shift from software-only workflows to identity proofing hardware must take place. Trustswiftly’s ial3 identity verification software offers the cryptographic certainty necessary to remove DPRK proxy networks, expose synthetic deepfakes and restore trust within federal supply chains.
NIST SP 800-63-4 presents high assurance identity verification requirements designed to meet the security and usability demands of modern workplaces. It prioritizes stronger authentication protocols like FIDO Passkeys while downgrading email OTPs and SMS to lower levels of assurance. In addition, this version mandates using federated assertion binding and cryptographic verification processes.
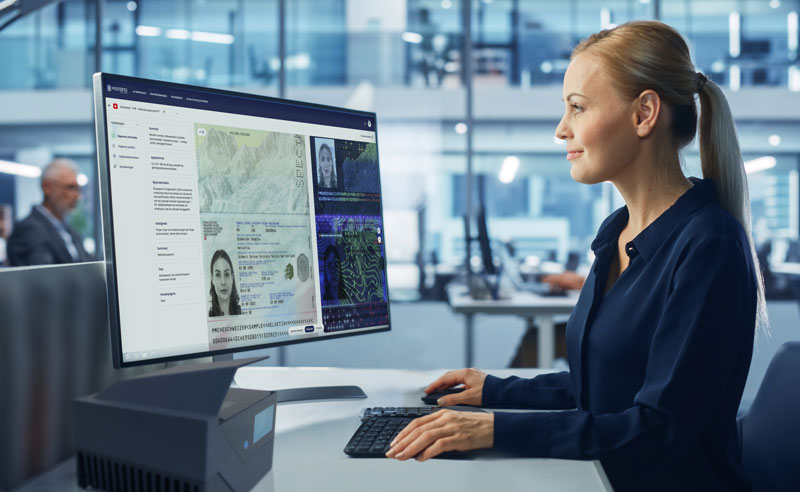
TrustSwiftly makes nist 800-63-4 ial3 compliance standards straightforward through a scalable, remote yet supervised process that integrates chat, video streaming and facial recognition technology with liveness detection or document authentication. This technology helps CSPs reduce attack surfaces, cyber liability insurance costs and operational expenses from reduced password reset requests and call center support calls; translating into real cost savings for their organization. NIST IAL3 standard represents the highest level of identification assurance, and requires on-site attended verification between two real humans to unequivocally establish someone’s digital identity thereby mitigating impersonation attacks, SIM swapping or MFA bypasses.
FedRAMP High Identity Proofing
The FedRAMP Security Baseline establishes minimum requirements that cloud providers must fulfill when working with government agencies. It includes an outline for onboarding federal customers with an emphasis on security by design and continuous controls validation – this helps reduce time and costs while freeing both parties up for innovation and growth.
FedRAMP compliance demands an in-depth and rigorous audit by an external party, along with ongoing vulnerability scans, incident reports, and annual reassessments. All these activities require considerable resources from your teams; Tenable One helps reduce this administrative overhead by centralizing reporting, threat detection and mapping security standards into one platform – turning continuous management and maintenance of critical environments (CMMC) into a continuous process that reduces risks while supporting secure-by-design practices.
FedRAMP authorization levels (Low, Moderate and High) vary based on the sensitivity and impact of data being protected and breached systems. Low authorization level should be sufficient for public-facing websites with non-sensitive information and public websites that do not need protection; moderate level is used by most federal systems handling controlled unclassified information (CUI); high level authorization should only be applied to emergency services, law enforcement systems with forensic data collection capabilities, healthcare systems that contain protected health data as well as national security systems.
An achievement of fedramp high identity proofing enables organizations to future-proof their deployments by meeting stricter requirements and creating more resilient security against advanced threats. Furthermore, this accreditation gives access to multiple federal agencies through the FedRAMP marketplace allowing economies of scale and faster return on investment for your enterprise.
NIST 800-63-4 IAL2 Software Benefits
IAL2 identity proofing requires additional evidence collection, validation, and verification requirements to protect against more sophisticated attacks than those addressed by IAL1 (e.g., falsification, theft, repudiation and social engineering tactics). Sessions for proofing with a trained CSP representative (proofing agent) take place onsite not remotely unattended with one or more biometric characteristics being collected as proofs.
The requirements of IAL2 include more stringent threat mitigations, such as out-of-band engagement with applicants through confirmation codes, checks against vital statistics repositories (e.g., Death Master File), fraud analysis capabilities that detect suspicious patterns of behavior, and verification pathways that do not rely on automated comparison of biometric samples but instead employ manual nist ial3 verification strategies utilizing evidence presented to proofing agents and identity proofing results provided to RPs.
For IAL2, sending out-of-band confirmation codes via verified channels offers an effective deterrent against scaled attacks against identity proofing processes and significantly decreases attacker time-to-value. Furthermore, it protects RPs from impersonation attacks during the process; and ensures protection for impersonation attempts against them during impersonation attacks during authentication events (subscriber-controlled wallets and PKI credentials on smart cards for instance). Furthermore, SUPERIOR evidence offers more security.
NIST 800-63-4 IAL1 Software Benefits
Besides providing technical requirements in identity proofing, enrollment, authenticators, management processes, authentication protocols and federation, this standard also outlines performance metrics organizations SHOULD track as part of their continuous evaluation programs. While individual organizations’ available metrics will depend upon their technologies, architectures and deployment methods; guidance is also included that may help those considering which metrics to track.
SP 800-63-4’s latest version introduces IAL1 as a new assurance level and updates authentication risk and threat models to account for emerging attacks as well as requirements that prohibit automated attacks during enrollment processes. Furthermore, it restructures this document so as to focus on each component of digital authentication assurance:
This revision transforms digital identity guidance from one document describing authentication (SP 800-63-1) into four documents that separately outline each assurance level: IAL, AAL, FAL, and federation assurance levels. This allows more independent treatment of each assurance level with regards to attack protections while also permitting agile development of the suite of four.